Indian Mujahideen: The Shocking Truth behind the Most Notorious Terrorist Organisation in India by Brij Lal | Goodreads
Mujahid Bakht Unveils AI Secrets in 'Silicon Success: How to Earn with AI and ChatGPT' - Betterauds.com

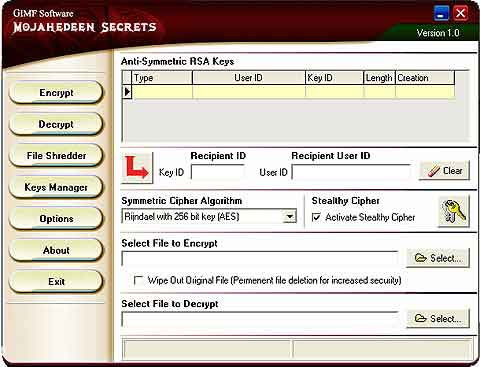
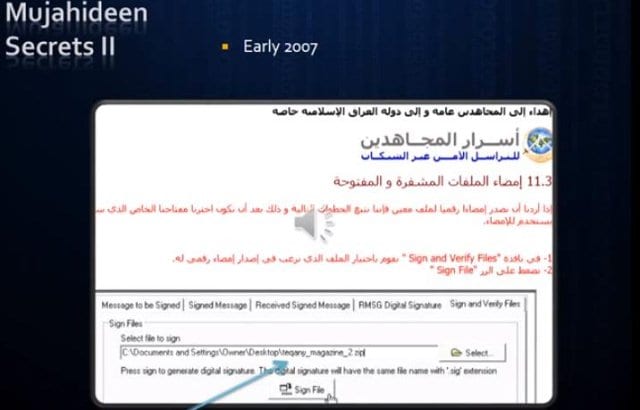
According to French "terrorism expert" Roland Jacquard, this manual, called "Mujahideen Secrets 2" is used by terrorists to avoid being tracked on the internet : r/programming

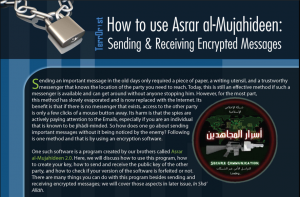
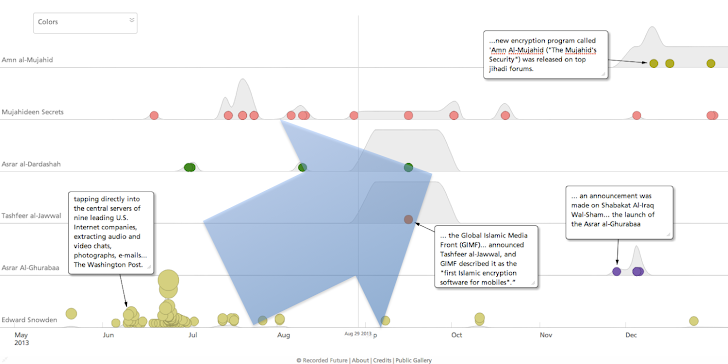
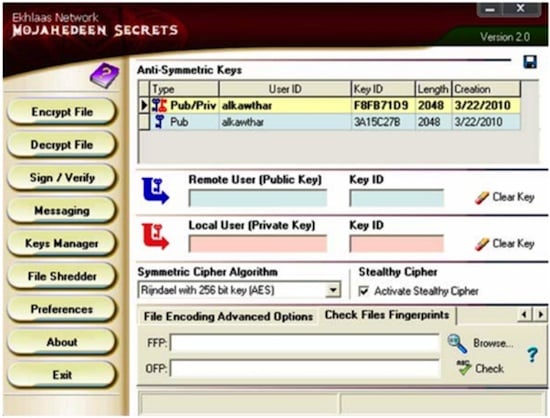
Al-Qaeda's Embrace Of Encryption Technology - Part II: 2011-2014, And The Impact Of Edward Snowden | MEMRI